Contents
|
|
Blockchain Applications complete review. The early internet dealt with intangibles. You sent or received emails, corresponded on forums, read and distributed articles. This modern internet deals with assets, your most valuable immediate items that you can touch and want to protect. These assets are stored in encoded form on a network-to-network chain called the blockchain or ledger, where each participant sees who you do business with. This not only protects your business dealings and prevents theft, but, also, simplifies your affairs, quickens the process, reduces errors, and saves you from hiring a third party.
This decentralized blockchain system is going to change your life from the way you transact business or manage assets, to the way you use your machines, vote, rent a car, and even prove who you are. Along the way, it will transform banks and other financial institutions, hospitals, companies, and governments among others.
If you are looking to create your own applications, please check out our blockchain courses.
Contents
Here’s what the blockchain does and what it means to you.
Blockchain Finance
Decentralized cryptocurrencies
At its simplest, cryptocurrencies, or digital coins, are coins that are passed through an electronic network. You can make transactions by check, wiring, or cash. You can also use a type of virtual currency, most famously Bitcoin (BTC) but also Litecoin, Peercoin, or Dogecoin, among others, where you use an electronic coded address to make the transaction.
The more valuable the transaction, the more you want to protect it. Traditional systems hire a mediator, such as a banker or a remittance company to ensure trust. Islanders of Yap had a different solution. They kept a mental record of who owned what and referred to this distributed community record when disputes arose. The blockchain is this community record on a wider, digital scale. It extends across the globe, with computer users from Yemen, Rome, Vermont and so forth where each node in the network records and verifies the data of each transaction that occurs within the network. Records are permanent, comprehensive and public – which is why users love the blockchain for finagling questionable or risky transactions.
How it works
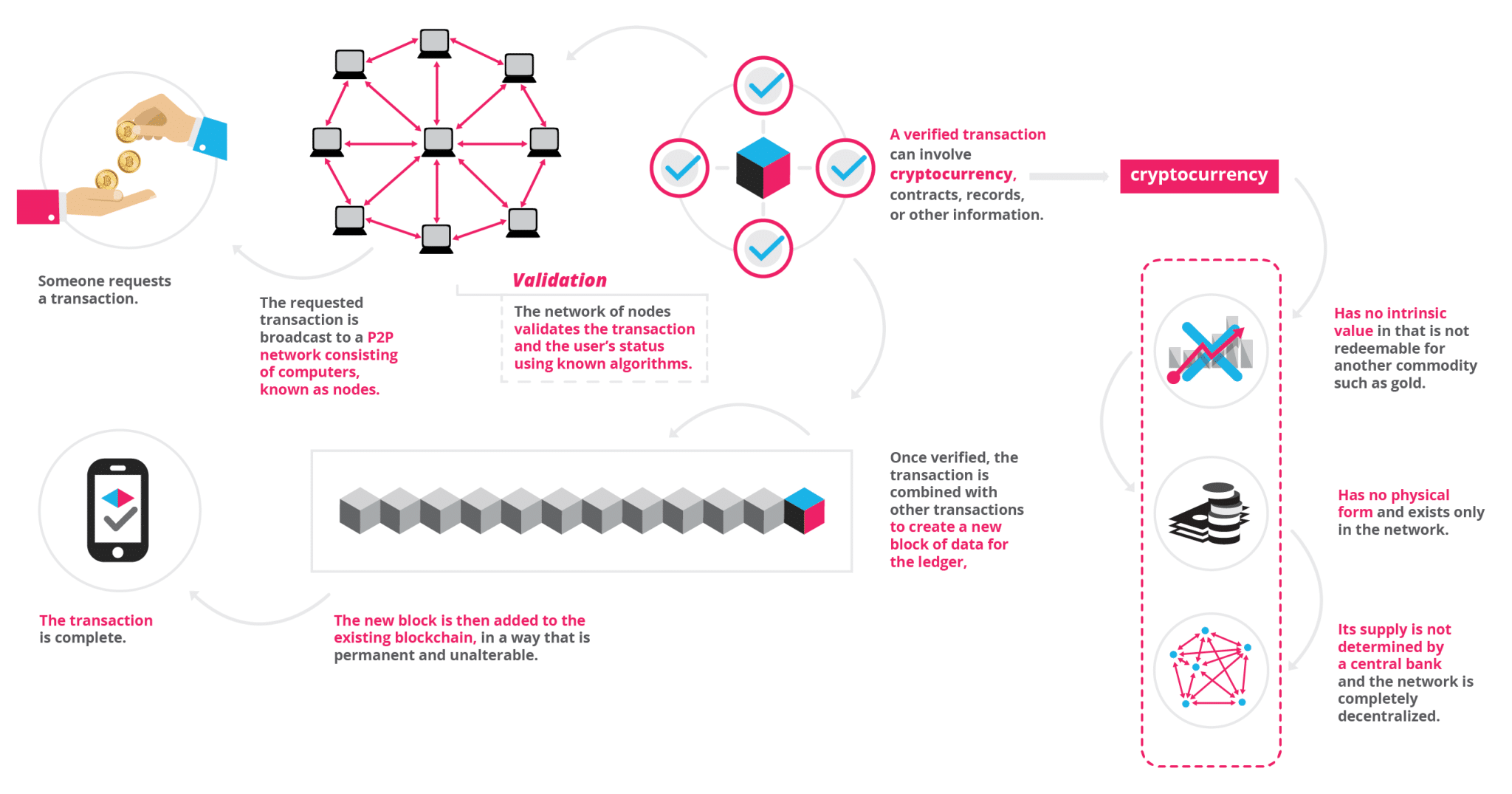
Each transaction is a digital ‘block’ that needs to be verified before it’s allowed to enter the system.
Questions include:
- Is the money there?
- Are sender and receiver reputable?
- Is the request legitimate? And so forth.
Each computer on the network competes on unscrambling the answers, and the winning computer adds this ‘block’ to the ‘blockchain’ in the order that the ‘block’ arrived. The winner broadcasts his proof to the rest of the network, which checks that proof and verifies it before queuing the ‘block’ to complete the transaction. Parties involved are assured that participants have screened and okayed the transaction.
The process not only cuts down on fraud, such as double spending or spams, but also transfers funds simply, safely, and fast.
17 Uses of Blockchain Applications That Are Transforming Society
- Asset Management: Trade Processing and Settlement
- Insurance: Claims processing
- Payments: Cross-Border Payments
- Unconventional money lenders/ hard money lending
- Your car/ smartphone
- Blockchain Internet-of-Things (IoT)
- Smart Appliances
- Supply Chain Sensors
- Blockchain Healthcare
- Blockchain music
- Blockchain Government
- Public value/ community
- Vested responsibility
- Blockchain Identity
- Passports
- Birth, wedding, and death certificates
- Personal Identification
Blockchain Business
Financial Services
Traditional systems tend to be cumbersome, error-prone and maddeningly slow. Intermediaries are often needed to mediate the process and resolve conflicts. Naturally, this costs stress, time, and money. In contrast, users find the blockchain cheaper, more transparent, and more effective. Small wonder that a growing number of financial services are using this system to introduce innovations, such as smart bonds and smart contracts. The former automatically pays bondholders their coupons once certain preprogrammed terms are met. The latter are digital contracts that self-execute and self-maintain, again when terms are met.
Examples of blockchain financial services applications
-
- Asset Management: Trade Processing and Settlement
Traditional trade processes within asset management (where parties trade and manage assets) can be expensive and risky, particularly when it comes to cross-border transactions. Each party in the process, such as broker, custodian, or the settlement manager, keeps their own records which create significant inefficiencies and room for error. The blockchain ledger reduces error by encrypting the records. At the same time, the ledger simplifies the process, while canceling the need for intermediaries. - Insurance: Claims processing
Claims processing can be a frustrating and thankless procedure. Insurance processors have to wade through fraudulent claims, fragmented data sources, or abandoned policies for users to state a few – and process these forms manually. Room for error is huge. The blockchain provides a perfect system for risk-free management and transparency. Its encryption properties allow insurers to capture the ownership of assets to be insured. - Payments: Cross-Border Payments
- Asset Management: Trade Processing and Settlement
The global payments sector is error-prone, costly, and open to money laundering. It takes days if not longer for money to cross the world. The blockchain is already providing solutions with remittance companies such as Abra, Align Commerce and Bitspark that offer end-to-end blockchain powered remittance services. In 2004, Santander became one of the first banks to merge blockchain to a payments app, enabling customers to make international payments 24 hours a day, while clearing the next day.
Smart Property
A tangible or intangible property, such as cars, houses, or cookers, on the one hand, or patents, property titles, or company shares, on the other, can have smart technology embedded in them. Such registration can be stored on the ledger along with contractual details of others who are allowed ownership in this property. Smart keys could be used to facilitate access to the permitted party. The ledger stores and allows the exchange of these smart keys once the contract is verified.
The decentralized ledger also becomes a system for recording and managing property rights as well as enabling the smart contracts to be duplicated if records or the smart key is lost.
Making property smart decreases your risks of running into fraud, mediation fees, and questionable business situations. At the same time, it increases trust and efficiency.
Examples of Blockchain Smart Property Applications
- Unconventional money lenders/ hard money lending
Smart contracts can revolutionize the traditional lending system. For instance, unconventional money lenders (e.g. hard money lenders) service borrowers who have poor credit with needed loans – while charging two to ten percent of the loan amount and claiming their property as collateral. Too many borrowers fall into bankruptcy and lose homes. The blockchain can undercut this by allowing a stranger to loan you money and taking your smart property as collateral. No need to show the lender credit or work history. No need to manually process the numerous documents. The property’s encoded on the blockchain for all to see. - Your car/ smartphone
Primitive forms of smart property exist. Your car-key, for instance, may be outfitted with an immobilizer, where the car can only be activated once you tap the right protocol on the key. Your smartphone too will only function once you type in the right PIN code. Both work on cryptography to protect your ownership.The problem with primitive forms of smart property is that the key is usually held in a physical container, such as the car key or SIM card, and can’t be easily transferred or copied. The blockchain ledger solves this problem by allowing blockchain miners to replace and replicate a lost protocol. - Blockchain Internet-of-Things (IoT)
Any material object is a ‘thing.’ It becomes an internet of things (IoT) when it has an on/ off switch that connects it to the internet and to each other. By being connected to a computer network, the object, such as a car, become more than just an object. It is now people-people, people-things, and things-things. The analyst firm Gartner says that by 2020 there will be over 26 billion connected devices. Others raise that number to over 100!How does the IoT affect you? Your printer can automatically order cartridges from Amazon when it runs low. Your alarm clock will change your time for brewing coffee, while your oven will produce an immaculately timed turkey for Thanksgiving. These are just some examples. On a larger scale, cities and governments can use IoT to develop cleaner environments, more efficient energy use and so-called ‘smart cities,’ to improve how we live and work.
Where the blockchain comes in
As in all cases, the blockchain ledger provides security to this Internet of things. With billions of devices linked together, cybersecurity experts worry how to make sure this distributed information stays secure.
- What can companies do to protect their systems from being invaded?
- How can inventors shield their ideas?
- How should governments protect their secret information from spies and potential terrorists?
Then, there’s the problem of how to organize and analyze this massive amount of data that’s coming from these related devices.
Enter the blockchain ledger system that ensures that information is only accepted and released to trusted parties. The ledger grants parties a management platform for analyzing the vast amounts of data.
Examples of Blockchain Internet-of-Things (IoT) Applications
- Smart Appliances
A smart appliance is a device that connects to the internet and gives you more information and control than before. For instance, a code connected to your appliance can be linked to the internet and alert you when your cookies are ready or if your laundry has stopped. These alerts keep your appliances in good condition, they save you money regarding energy efficiency and help you control your devices when away from home, among other benefits. Encrypting these appliances on the blockchain protects your ownership and enables transferability. - Supply Chain Sensors
Sensors give companies end-to-end visibility of their supply chain by providing data on the location and condition of the supplies as they are transported around the globe. As of 2016, a Deloitte and MHI report surveyed 99 leading supply chain companies and found that sensors were used by 44% of these respondents. Eighty-seven percent of these industries said they plan to use the technology by 2020. The technology is expected to grow to 1 trillion by 2022 and to 10 trillion sensors by 2030, according to this sme Deloitte and MHI report. The blockchain stores, manages, protects and transfers this smart information.
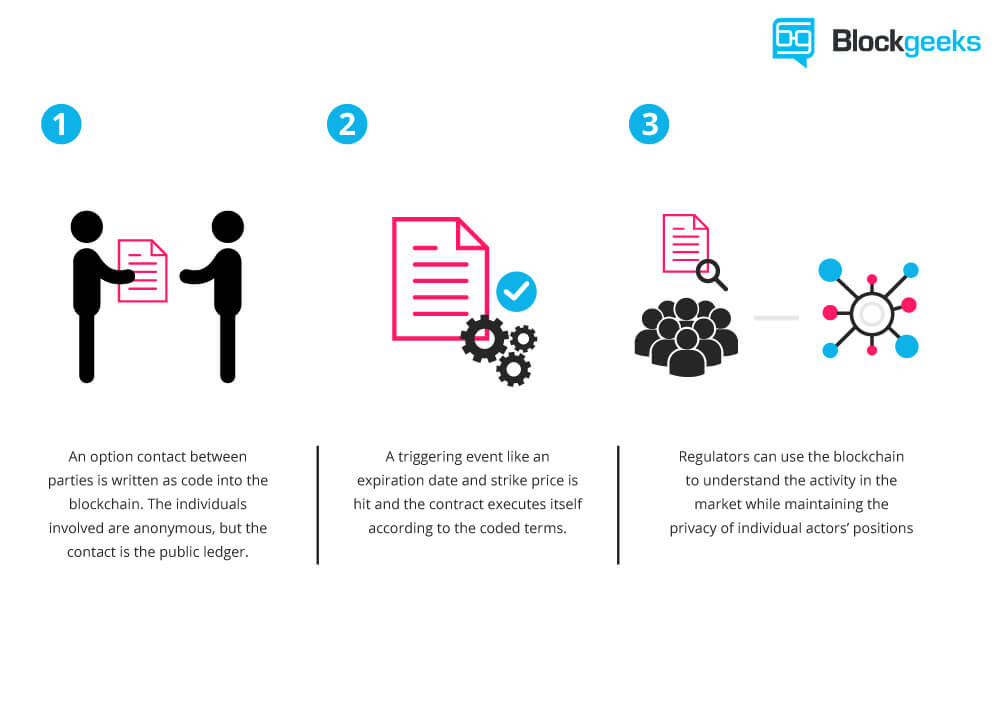
Smart Contracts
Smart contracts are digital which are embedded with an if-this-then-that (IFTTT) code, which gives them self-execution. In real life, an intermediary ensures that all parties follow through on terms. The blockchain not only waives the need for third parties, but also ensures that all ledger participants know the contract details and that contractual terms implement automatically once conditions are met.
You can use smart contracts for all sort of situations, such as financial derivatives, insurance premiums, property law, and crowd funding agreements, among others.
Examples of Blockchain Smart Contracts Applications
- Blockchain Healthcare
Personal health records could be encoded and stored on the blockchain with a private key which would grant access only to specific individuals. The same strategy could be used to ensure that research is conducted via HIPAA laws (in a secure and confidential way). Receipts of surgeries could be stored on a blockchain and automatically sent to insurance providers as proof-of-delivery. The ledger, too, could be used for general health care management, such as supervising drugs, regulation compliance, testing results, and managing healthcare supplies. - Blockchain music
Key problems in the music industry include ownership rights, royalty distribution, and transparency. The digital music industry focuses on monetizing productions, while ownership rights are often overlooked. The blockchain and smart contracts technology can circuit this problem by creating a comprehensive and accurate decentralized database of music rights. At the same time, the ledger and provide transparent transmission of artist royalties and real time distributions to all involved with the labels. Players would be paid with digital currency according to the specified terms of the contract. - Blockchain Government
In the 2016 election, Democrats and Republicans questioned the security of the voting system. The Green Party called for a recount in Wisconsin, Pennsylvania, and Michigan. Computer scientists say hackers can rig the electronic system to manipulate votes. The ledger would prevent this since votes become encrypted. Private individuals can confirm that their votes were counted and confirm who they voted for. The system saves money, by the way, for the government, too.The blockchain ledger, also, provides a platform for what we call “responsive, open data.” According to a 2013 report from McKinsey and Company, open data – freely accessible government-sourced data that is available over the internet to all citizens – can make the world richer by $2.6 trillion. Startups can use this data to uncover fraudulent schemes, farmers can use it to perform precision farm-cropping, and parents can investigate the side effects of medicine for their sick children. Right now, this data is released only once a year and is, largely, non-responsive to citizens input. The blockchain, as a public ledger, can open this data to citizens whenever and wherever they want.
Examples of Blockchain Government Applications
- Public value/ community
The blockchain can facilitate self-organization by providing a self-management platform for companies, NGOs, foundations, government agencies, academics, and individual citizens. Parties can interact and exchange information on a global and transparent scale – think of Google Cloud, but larger and less risky. - Vested responsibility
Smart contracts can ensure that electorates can be elected by the people for the people so that government is what it’s meant to be. The contracts specify the electorate’s expectations and electors will get paid only once they do what the electorate demanded rather than what funders desired. - Blockchain Identity
Whether we like it or not, online companies know all about us. Some companies whom we purchase from sell our identity details to advertisers who send you their ads. The blockchain blocks this by creating a protected data point where you encrypt only the information that you want relevant people to know at certain times. For example, if you’re going to a bar, the bartender simply needs the information that tells him you’re over 21.
Blockchain Identity
The blockchain protects your identity by encrypting it and securing it from spammers and marketing schemes.
Examples of Blockchain Identity Applications:
- Passports
The first digital passport launched on Github in 2014 and could help owners identify themselves online and off. How does it work? You take a picture of yourself, stamp it with a public and private key, both of which are encoded to prove it is legitimate. The passport is stored on the ledger, given a bitcoin address with a public IP, and confirmed by Blockchain users. - Birth, wedding, and death certificates
Few things are more important than documents showing you’re born, married, died which open your rights to all sorts of privileges (such as voting, working, citizenship), yet mismanagement is rife. Up to a third of children under the age of five have not been issued a birth certificate, the UNICEF reported in 2013. The blockchain could make record-keeping more reliable by encrypting birth and death certification and empowering citizens to access this crucial information. - Personal Identification
We carry a range of identifications: Our driver’s license, computer password, identity cards, keys, social security ID, and so forth. Blockchain ID is a digital form of ID that’s engineered to replace all these forms of physical identification. In the future, fintech scientists say you’ll be able to use the one digital ID for signing up at any registrar. It is open source, secured by the blockchain, and protected by a ledger of transparent account.
Blockchain Applications: Conclusion
It’s important to note that for the blockchain to work, the node-to-node network must be motivated and agree to work under ethical standards. Once, and only if, these standards are adhered to, the blockchain could become a powerful tool for improving business, conducting fair trade, democratizing the global economy, and helping support more open and fair societies.




Here is the music one that I’m working on (in beta): https://musicoin.org/nav/main