Is Silicon Valley Season 4 About Ethereum?
Spoiler alert: seems like it.
Serious hints were dropped in the trailer for the fourth season of HBO’s Silicon Valley. The first episode, released last Sunday, takes it to the next level. It’s official: brilliant but ill-fated startup founder Richard Hendricks is building a new, decentralized Internet with “Ethereum-type computer”.
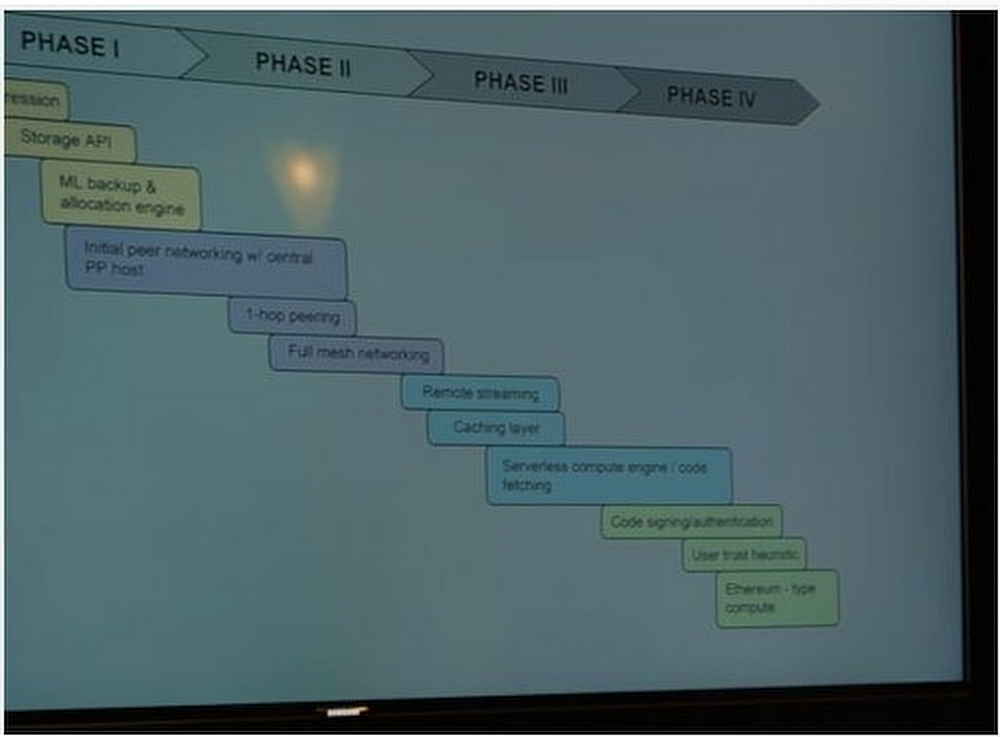
Silicon Valley Season 4 is all about decentralized tech. Whoop! See phase IV -> “Ethereum-type compute”. pic.twitter.com/2ocHQZJ3qB
— Simon de la Rouviere (@simondlr) March 29, 2017
What is Ethereum?
Ethereum is a decentralized world computer that enables peer-to-peer transactions and the execution of smart contracts. It allows people to frictionlessly exchange and communicates, with no intermediaries. In other words, ethereum is the next generation of the Internet.
Why is ethereum on Silicon Valley?
Even if not by name, Silicon Valley has consistently referenced blockchain and cryptocurrency.
In the previous season, Pied Piper was already exploring the theme of decentralization. They set up their video platform to work like BitTorrent or IPFS where decentralized storage increases the total availability of artifacts and localizes bandwidth requirements.
Netflix has explored this idea, because every time a large number of people want to watch the same program at once, it wastes Internet bandwidth. If everyone is watching Stranger Things, they are all streaming copies of the same content from their servers, from a centralized place to a bunch of decentralized places.
If Netflix allowed storage on devices, and peer-to-peer downloads, the bandwidth of the Internet could be used more effectively, representing huge cost savings for the company.
This idea is the basis of the video compression and streaming app Pied Piper developed on the third season of Silicon Valley. Not only that, but the team buys a bunch of mining hardware (a staple of the blockchain and cryptocurrency world) and sets it up in the garage as part of the infrastructure they use to produce the compression.
Arguably the character Richard Hendricks is already exploring the ideas of decentralization anyway when he’s prompted in Season 4 Episode 1 by a (last ditch) potential investor to explain what he really wants to do. He says:
“We could build a completely decentralized version of our current Internet, with no firewalls, no tolls, no government regulation, no spying. Information would be totally free, in every sense of the word.”
ethereum plus IPFS is one way to realize that goal. Then the product roadmap Hendricks draws on a whiteboard says “Ethereum-type compute”.
Let’s break it down.
- “a completely decentralized version of our current Internet.”
There are no central points of control on ethereum. However, some think that the U.S. government has an “Internet kill switch” in Langley, Virginia where the CIA is located. Kill switch aside; it’s possible for authorities to control Internet access or shut it off in certain geographical areas.
The original architects of the Internet, however, were thinking in a fairly decentralized way. As John Gilmore, one of the founders of the Electronic Frontier Foundation said, “The Internet interprets censorship as damage and routes around it.”
This is representative of how people were thinking about the Internet in its early days. That’s why DNS, for instance, has a decentralized architecture. Similarly, the Border Gateway Protocol, which allows computers on the Internet to exchange routing and reachability information, functions in a decentralized way.
Administrations in the U.S. and beyond have attempted to centralize control, and obviously, in some countries, they have succeeded. On the other hand, the protocols that run ethereum are impervious to central control.
2. “with no firewalls, no tolls, no government regulation, no spying.”
The forces that have been able to centralize control of the Internet as it exists today would be unable to centralize control of ethereum.
Frighteningly, few people know about the small group of people who meet in person in order to secure the Internet. The continued function of the Internet depends on a centralized group of seven human “key holders.”
There is no such mechanism on ethereum.
“No firewalls” and “no spying” are related. Firewalls are a typical manifestation of perimeter defense, which is what traditional security architecture depends upon. Firewalls prevent access to assets that sit behind servers. To get to Google, you have to get through their firewall. But once you get past the firewall, there are many ways to begin compromising accounts and gaining control of the systems within.
In the case of ethereum, every transaction has to be signed by a cryptographic key. In theory, each key is only owned by its rightful owner. So there is no need for perimeter defense, because no action can be taken that is not granularly authorized.
In a world where people have control over cryptographic keys (as users do in uPort) and granularly authorize every action with a cryptographic signature, what emerges is a public key infrastructure that extends to every user of the system.
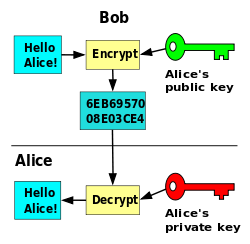
Right now, the public key infrastructure that secures web traffic is centralized, meaning that only trusted root certificate authorities (like VeriSign) are able to give public-private key pairs to organizations that are trusted (like your bank). For the most part, Individuals don’t have public key infrastructure regularly accessible to them.
This is a barrier to all communication being encrypted, because the process of setting up the encrypted channel is difficult without a public key infrastructure. So: if every action were not only granular, but every action in its transmission were also encrypted in some way using that public key infrastructure, then spying would literally be impossible.
On the public Ethereum network right now, you could spy on the transactional behavior as it propagates through the network, but with the integration of zk-SNARKs, for instance, it will be impossible to spy on the Ethereum system.
3. “information would be totally free.”

The structure of the Internet today restricts the free flow of information in a few different ways: data silos, intermediaries, and lack of incentive to make the information public.
To interact with Internet services, we need an identity, which is usually provided by Google or Facebook. These data vendors (and many, many others) collect your personal information, store it in private servers, and leverage it in several ways, notably by selling it to advertisers.
On the decentralized Web 3.0 enabled by Ethereum, users will have access to self-sovereign identity with platforms such as uPort, allowing them to collect rich data sets connected to their personal cryptographic keys that they alone control.
Users can selectively reveal, conceal, or sell this information as they see fit, directly to their peers without any kind of intermediary coming between counterparties that could restrict its free flow. No central authority would be required to approve any exchange of information.
Platforms such as Gnosis, the prediction market built on Ethereum, incentivize users of the decentralized Web to share their knowledge with the world, and to help predict the outcomes of events. Prediction markets have been shown to better forecast discrete outcomes than experts, polls, and projections. Gnosis or a similar platform creates an incentive structure to extract high-quality information from users and make it available to the public.
Originally published on Medium.
Nice write-up Sam. I did see this episode on last Sunday and I had concluded the same thing. They were talking about the blockchain technology. They must have some forward thinking consultants advising the writers.