Contents
|
|
In this guide you will learn why most ICO’s Will Fail..
On June 12, 2017, an Ethereum based called Bancor held its ICO. It raised $153 million in 3 hours. No, you are not reading it wrong, 153 million…..in 3 hours!!!
If that doesn’t get your brain melting, then how about this? The BAT ICO $35 million in 30 seconds!!! That’s near $1.2 million per second! And if that still doesn’t get your jaw dropping, then how about this? Have you heard of UET? UET had an ICO which raised $40,000 in just 3 days. Admirable if not particularly mind-blowing. Why do we bring it up after talking about Bancor and BAT?
Well, UET stands for “Useless Ethereum Token”, it is a “joke coin”.
Here is the sales pitch that they used, “UET is a standard ERC20 token, so you can hold it and transfer it. Other than that… nothing. Absolutely nothing.” And they raised $40,000 in 3 days! Welcome to the crazy world of ICOs! There is no doubt that ICOs have changes the financial landscape over the past 2 years. In the first half of 2017 alone they raised over $1 billion!
However, all these insane success stories tend to make us look at facts with rose-tinted glasses. The fact is, that around 99% of all ICOs out there will fail. And that’s not exaggerated doom and gloom, over the last few years, thousands of cryptocurrencies have been created and over 90% of them have failed. And the fact also remains that given the insane success of most ICO’s, scammers are flooding the market creating bogus dapps/coins to get their fill of the ICO pie and effectively create an “ICO bubble”.
So, keeping all this in mind let’s aim to answer this simple question: “Why are most of the ICOs going to fail?”
A quick disclaimer before we continue
Before we continue, we want to make something very clear. We don’t “hate” on ICOs. We believe that ICOs are truly revolutionary and will continue to evolve and will become an amazing vehicle for developers, entrepreneurs and investors who are looking to innovate and change the world by just showing their concept aka a whitepaper. (Well, we hope more than just a whitepaper) That’s truly brilliant. 🙂
With that being said, let’s start.
Contents
Why Most ICO’s Will Fail: A Cold Hard Truth
So, how does an ICO work?
Firstly, the developer issues a limited amount of tokens. By keeping a limited amount of tokens they are ensuring that the tokens itself have a value and the ICO has a goal to aim for. The tokens can either have a static pre-determined price or it may increase or decrease depending on how the crowd sale is going.
Tokens are basically native currencies that can be used in an environment (think of the arcade coins that you needed to play games in an arcade) or they give their owners various rights inside the native environment (Think of the wristbands that certain nightclubs use which entitles you to get a certain number of free drinks).
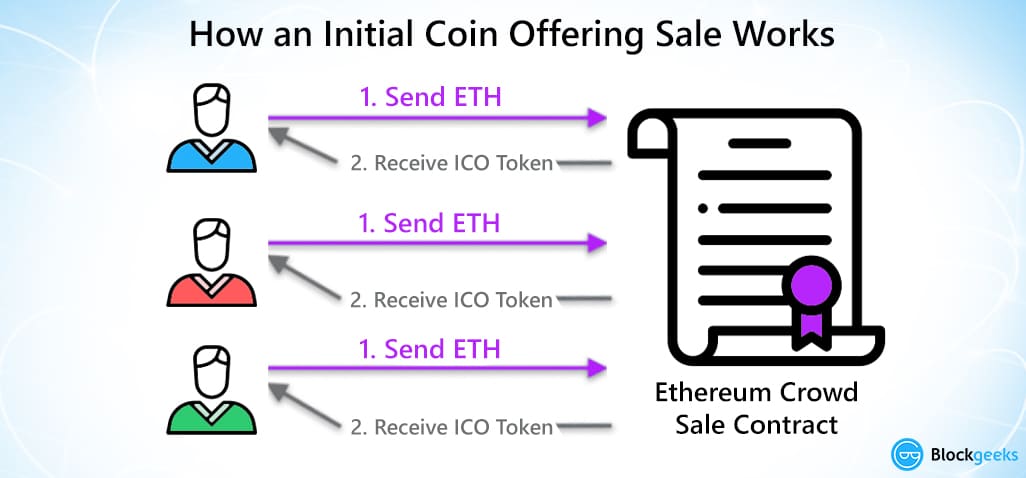
The transaction is a pretty simple one. If someone wants to buy the tokens they send a particular amount of ether to the crowd-sale address. When the contract acknowledges that this transaction is done, they receive their corresponding amount of tokens.
So, that’s a general idea on how ICOs works. But then why do most ICOs fail. The reason why most ICOs fail is that most developers/entrepreneurs do not pay any attention to the three pillars that make an ICO:
- Cryptoeconomics.
- Utility.
- Security.
Pillar #1: Cryptoeconomics
It is funny how most developers forget the “cryptoeconomics” of their ICOs. There are two words that makeup cryptoeconomics: “cryptography” and “economics”. While most developers pay attention to the cryptography part, they hardly pay any attention to the “economics” part. As a result of which, it is very rare to find a token whose economic skeleton has been properly and thoroughly mapped out.
In order for the token to be decently valuable in the long run, there must be sufficient demand for it but that is not what is usually seen in the ICOs. What is seen is unsustainable token inflation which largely happens because of flawed economic models and the greater fool theory (more on that in a bit).
For these permanently inflationary tokens, their demand must always outpace their inflation for them to be valuable in the long run, which more often than not creates a Ponzi Scheme like scenario.
Before we go into all that, however, we need to understand where the fundamental problem of most ICO economic model lies.
One of the biggest advantages of ICOs is that anyone can come and raise money for their concept…not a finished product, a concept. There is still a long way to go before that concept can become a product and as with anything, there is a 90-95% chance that it will be a failure.
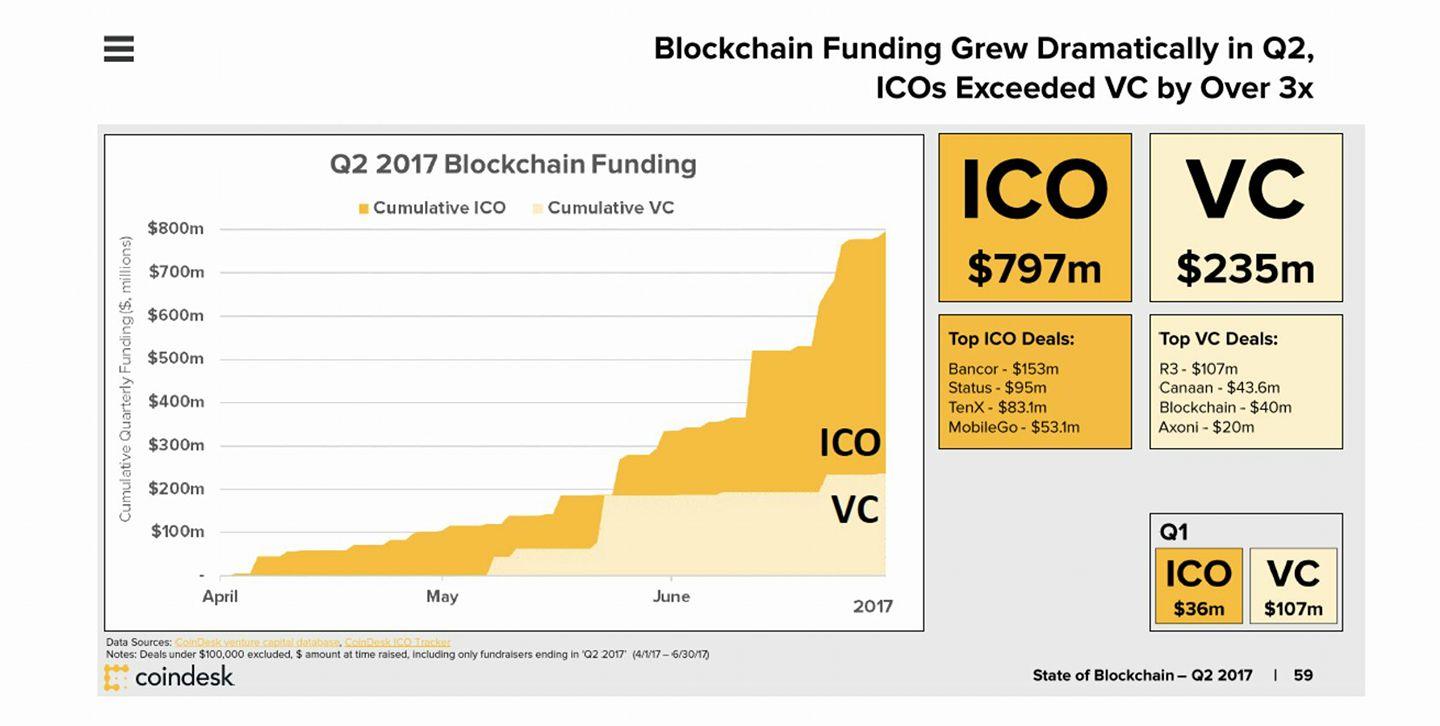
However, many of the early adopters of ICOs have made a killing because of the low entry and the high profit. As a result of this everyone else developed a massive case of FOMO (Fear Of Missing Out) and started pouring millions into concepts that didn’t even have an alpha version ready. Look at this, for instance, ICOs made nearly $800 million in the second quarter of 2017 alone! Compared to that, Venture capital made just $235 million:
These are people who have little to no idea about how the blockchain works, they are just putting in money to make a quick buck. Seeing this trend, the developers shifted their focus. Instead of making Dapps/currencies which added something new and unique to the ecosystem, they started making products for the ICO.
Their end goal became: “Build a flashy enough whitepaper to get good money in ICOs”. Because of this rampant speculation and very little due diligence, the “Greater Fool Theory” came into play.
What is the Greater Fool Theory?
The Greater Fool Theory is an economic theory which states that the price of an object increases not because of the value that it brings in but because of the irrational beliefs attached to it. Art is a great example of the greater fool theory.
So let’s apply the same to ICOs. You have a bunch of dapps and currencies coming up which are bringing in nothing new to the ecosystem. However, because they have been hyped up so much and there so many ignorant investors around, their value increases anyway, and as a result, the tokens face an inflation.
So, let’s recap what we have learned so far:
- Investors are investing millions into concepts that don’t even have an alpha version of their product.
- Investors are desperate to put their money in because they think that ICOs are a way to get rich quick.
- In order to cash in on this, developers are creating products more aimed towards ICOs than to give actual value.
- Because of the “Greater Fool Theory.” the value of the tokens gets inflated.
If this sounds suspiciously like a bubble then yes, you are right and the thing is, we have been here before, we have seen this play out. The whole ICO situation is scarily reminiscent of another wave that swept us in the late 90’s. They say that those who are not aware of history are bound to repeat it. So let’s do a quick history lesson and turn back the clocks.
The Dot-Com Bubble
Around 1997, the internet became big and tech companies began to emerge everywhere. Investors started putting in their money and flipping their investments into huge sums. Eventually, everyone who saw this started getting major FOMO (fear of missing out) and they began giving away their money to companies without even having any idea as to whether the business had the potential to work or not.
Common sense went out of the window and every random internet business was making a killing in the IPOs. Warren Buffet noted that:
“The fact is that a bubble market has allowed the creation of bubble companies, entities designed more with an eye to making money off investors rather than for them. Too often, an IPO, not profits, was the primary goal of a company’s promoters.”
BOOM!
He hit the nail right on the head, most of the companies that got millions from their investors failed and some turned out to be nothing more than scams. Eventually, the bubble burst in 2002. Companies crashed and lost millions within a year. One of the most infamous examples of this is Pets.Com which lost $300 million in just 268 days!
The parallels between the ICO bubble and the dot-com bubble are a bit frightening. Much like dot-coms, the ICOs have attracted a lot of investors who don’t want to miss out on the gold rush. Much like the dot-coms ALL the investing is done purely from speculation. You have to realize that most of the companies that you are investing in, in ICOs barely have anything ready. Most of them don’t have the alpha version of their end result, it is all based on speculation and the potential of the project.
As with anything, most of these projects will fail to get the end results. The reason why the Ethereum ICO worked so wonderfully was that it had a dedicated and driven team of talented developers who were a day in and day out to make it a success, same with Golem.
The parallels are very apparent and it can get real scary thinking about it. But we are not market experts. All we can do is speculate. We don’t know whether we are living in the “ICO bubble” or not, nor do we know whether it is a bubble that is going to pop.
What we do know is that unless developers stop with their “get rich quick schemes” and actually pay attention to launching ICOs which bring in true value and has a concrete economical skeleton, then we will be seeing patterns which are depressingly similar.
Pillar #2: Utility
What is the definition of Utility? Utility means the total satisfaction that is received by the consumption of the goods or services. Most of the ICOs do not maximize their token utility. The tokens should be absolutely integral to the ICO and must increase the overall value of your final product.
If you are an ICO developer, then ask yourself this question: If you take away your token does your business fall apart? If the answer is no, then you don’t need a token. There are only a few cases that make sense to tokenize. Most people get tokens only so they can “HODL” it and buy more bitcoin and ethereum in the future! Is that all that your tokens are worth?
If you do use tokens for your business, then you need to completely understand its role and maximize its utility. You have to understand that tokens can be multi-purpose tools which can bring in a lot of “oomph” to your business. Your business model should be such that you are exploiting your tokens to the maximum possible limit.
(Before we continue, we would like to give shoutouts to the inimitable William Mougayar and Kyle Samani for their brilliant work and research.)
As William Mougayar points out in his Medium article, there are three tenets to token utility and they are:
- Role.
- Features.
- Purpose.
These three are locked up in a triangle and they look like this:
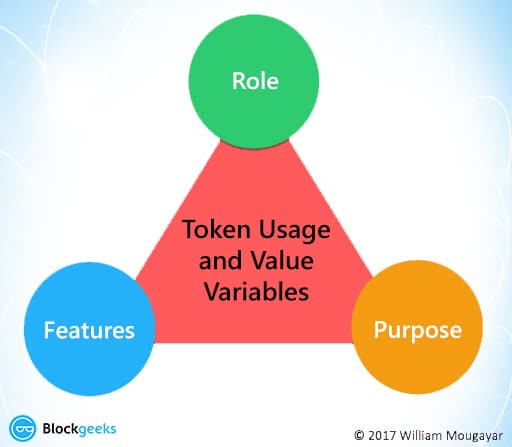
Each token role has its own set of features and purpose which are detailed in the following table:

Let’s examine each of the roles that a token can take up:
- Right
By taking possession of a particular token, the holder gets a certain amount of rights within the ecosystem. Eg. by having DAO coins in your possession, you could have had voting rights inside the DAO to decide which projects get funding and which don’t.
- Value Exchange
The tokens create an internal economic system within the confines of the project itself. The tokens can help the buyers and sellers trade value within the ecosystem. This helps people gain rewards upon completion of particular tasks. This creation and maintenance of individual, internal economies is one of the most important tasks of Tokens.
- Toll
It can also act as a toll gateway in order for you to use certain functionalities of a particular system. Eg. in Golem, you need to have GNT (golem tokens) to gain access to the benefits of the Golem supercomputer.
- Function
The token can also enable the holders to enrich the user experience inside the confines of the particular environment. Eg. In Brave (a web browser), holders of BAT (tokens used in Brave) will get the rights to enrich customer experience by using their tokens to add advertisements or other attention based services on the Brave platform.
- Currency
Can be used as a store of value which can be used to conduct transactions both inside and outside the given ecosystem.
- Earnings
Helps in an equitable distribution of profits or other related financial benefits among investors in a particular project.
So, how does this all help in token utility?
If you want to maximize the amount of utility that your token can provide then you need to tick off more than one of these properties. The more properties you can tick off, the more utility and value your token brings into your ecosystem. If the role of your tokens cannot be clearly explained, or if it doesn’t really tick off more than one of the roles given above, then your token doesn’t have any utility and you can do without it.
Now, let’s move onto another interesting concept called “Token Velocity”.
Token velocity in simple terms means: Are people going to hold on to the tokens for long-term gain or sell it off immediately? This is a problem with most ICO and token structures because they are being treated more as a vehicle for liquidation than as a store of long-term value. In fact, regarding this, Willy Woo did an interesting case study.
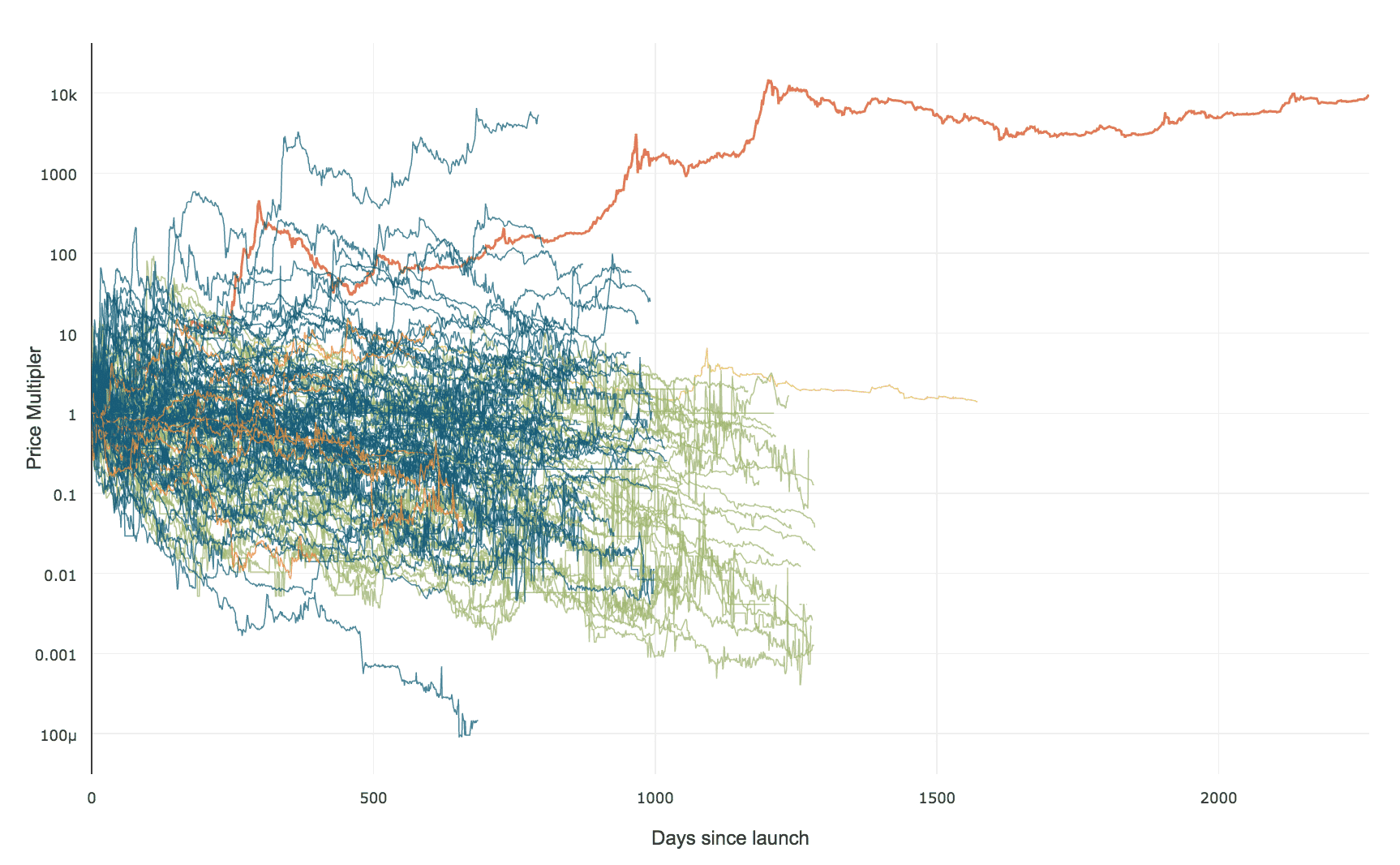
He plotted the performances of 118 coins, from the first day of their inception to the day he made the graph. His only qualification was this; the coin should have reached a market cap of at least $250,000 in any one year of its existence. Let’s see what he came up with:
Image courtesy: WooBull
See that red line soaring triumphantly over everyone else? That is bitcoin. It is the only crypto that has performed consistently and grown from strength to strength. (The blue line above the bitcoin line is a statistical aberration according to Woo).
In fact, Woo’s research becomes more interesting when you break it down even further. Here he has grouped the coins together according to the year of their inception. Let’s see how well the coins from each year group performed:
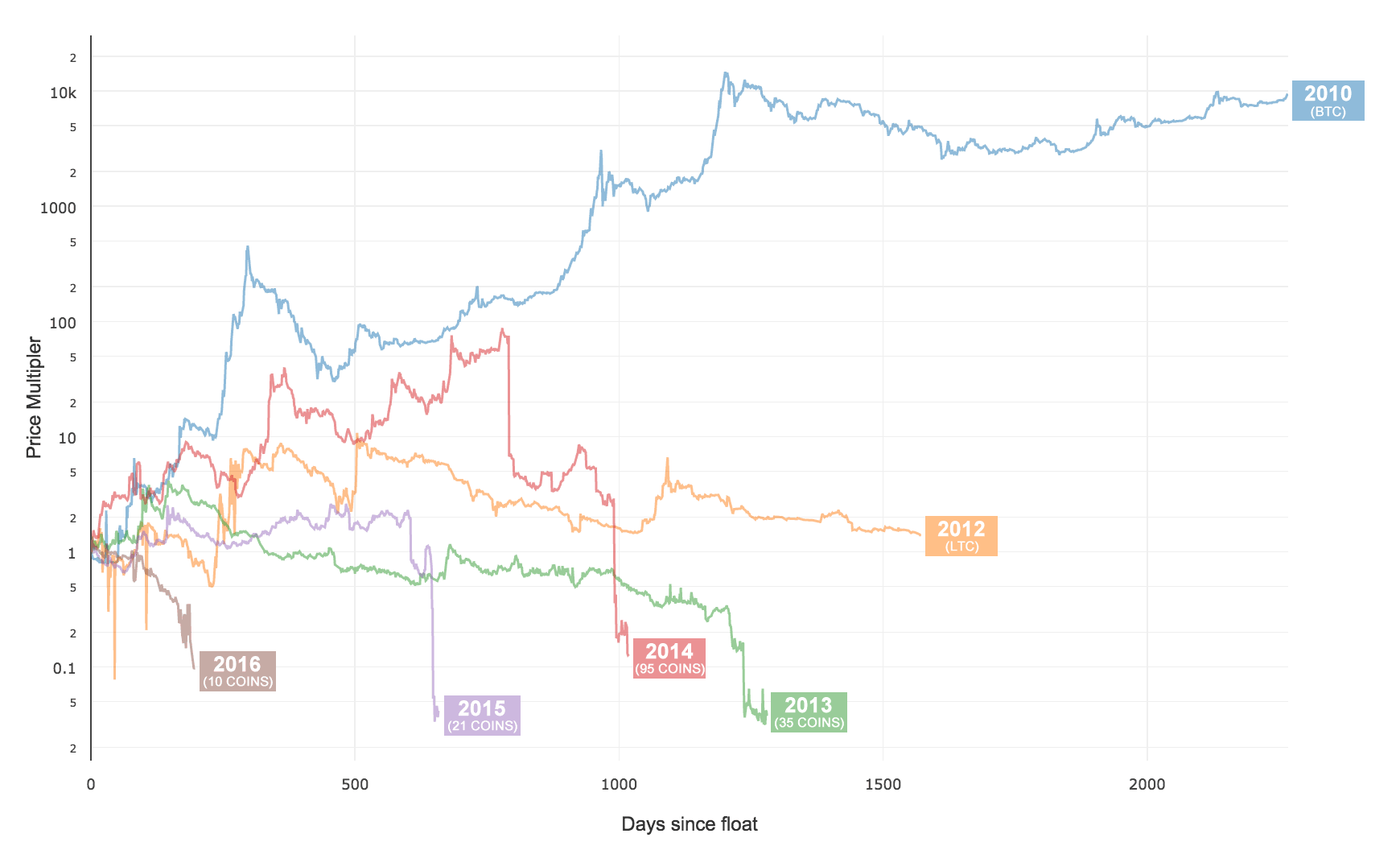
Image courtesy: WooBull
Yikes! That does not look good at all!
What this shows is that every year the coins are performing worse and worse. And the reason for that is simple. More and more scam ICOs are coming in and developers are not making valuable enough projects. As a result of which, we have tokens, which perform no other utility than being a means of liquidation and that is exactly why Bitcoin and ethereum are so far and above everyone else. People realize their potential as a proper long-term store of values.
This is exactly why developers need to pay attention to token velocity. The reason why Bitcoin and ethereum have such high values is because, they are low-velocity coins. Let’s quantify token velocity (TV):
Let’s quantify token velocity (TV):
TV = Total Trading Volume / Average Network Value.
So, more the trading volume aka more that coin is traded more the velocity. Consequently, less the network value, more the velocity.
Now if you examine this from the perspective of bitcoin, then you will know exactly why its velocity is less.
- No other crypto has as much network value as bitcoin.
- No one wants to trade off bitcoin because they know that there is value in holding it.
So, what should developers do to ensure that they have less token velocity? They need to work and re-examine their tokens. They need to understand whether a token is being fully utilized or not. They need to answer several questions, some of which are:
- Does my project really need a token?
- Am I fully exploiting the token and getting as much token utility as possible.
- Is my token useful only for initial liquidation purposes?
- Is there any value in holding my token long term?
- Is my token ticking off as many roles as possible?
It is only when developers work on the utility of their tokens will they be able to bring something which can contribute significantly to the ecosystem
Pillar #3: Security
And now we come to the third pillar… security
During your ICO and immediately after your ICO you have a big target on your back. If you haven’t paid attention to your security, hackers will attack you and they will rob you. In fact, this is what Chainanalysis had to say:
“More than 30,000 people have fallen prey to ethereum-related cyber crime, losing an average of $7,500 each, with ICOs amassing about $1.6 billion in proceeds in 2017.”
In fact, Chainanalysis claims that there is a 1 in 10 chance that you will end up a victim of the theft! That is staggering.
The crimes that happen largely fall into three categories:
- Faulty code.
- Phishing Schemes.
- Mismanagement of keys.
Faulty Code
Perhaps the most infamous example of this is the DAO attack.
The DAO aka the Decentralized Autonomous Organization was a complex smart contract which was going to revolutionize Ethereum forever. It was a decentralized venture capital fund which was going to fund all future DAPPS made in the eco-system.
The way it worked was pretty straightforward. If you wanted to have any say in the kind of DAPPS that would get funded, then you would have to buy “DAO Tokens” for a certain amount of Ether. The DAO tokens were indicators that you are now officially part of the DAO system and gave you voting rights.
If in case, you and a group of other people were not happy with the DAO then you could split from it by using the “Split Function”. Using this function, you would get back the ether you have invested and, if you so desired, you could even create your own “Child DAO”. In fact, you could split off with multiple DAO token holders and create your own Child DAO and start accepting proposals.
There was one condition in the contract, however, after splitting off from the DAO you would have to hold on to your ether for 28 days before you could spend them. And this was where the loophole was created. People saw this in advance and brought it up but the DAO creators assured that this was not going to be a big issue. They couldn’t have been more wrong.
The DAO Attack
On 17th June 2016, someone exploited this very loophole in the DAO and siphoned away one-third of the DAO’s funds. That’s around $50 million dollars. The loophole that the hacker(s) discovered was pretty straightforward in the hindsight.
If one wished to exit the DAO, then they can do so by sending in a request. The splitting function will then follow the following two steps:
- Give the user back his/her Ether in exchange of their DAO tokens.
- Register the transaction in the ledger and update the internal token balance.
What the hacker did was they made a recursive function in the request, so this is how the splitting function went:
- Take the DAO tokens from the user and give them the Ether requested.
- Before they could register the transaction, the recursive function made the code go back and transfer even more Ether for the same DAO tokens.
This went on and on until $50 million worth of Ether were taken out and stored in a Child DAO and as you would expect, pandemonium went through the entire ethereum community. The price of Ether dropped from $20 to $13 overnight. This still remains the worst ICO hack ever. The aftermath of the hack was so extreme that it split ethereum into two different currencies: Ethereum and Ethereum Classic.
Phishing Schemes
Here is something truly scary for you to wrap your head around.
Phishing scams have stolen up to 5 million in ethereum related cybercrimes. In fact, as we have mentioned before, more than 30,000 people have fallen prey to ethereum-related cyber crime, losing an average of $7,500 each.
So, before we continue, what is phishing?
Phishing is the process by which scammers get your sensitive information (like credit card details) by impersonating someone trustworthy and of notable repute. The scammers usually use email and in some cases, they use social media. In fact, someone has been trying to phish ICO developers by impersonating our very own Ameer Rosic!
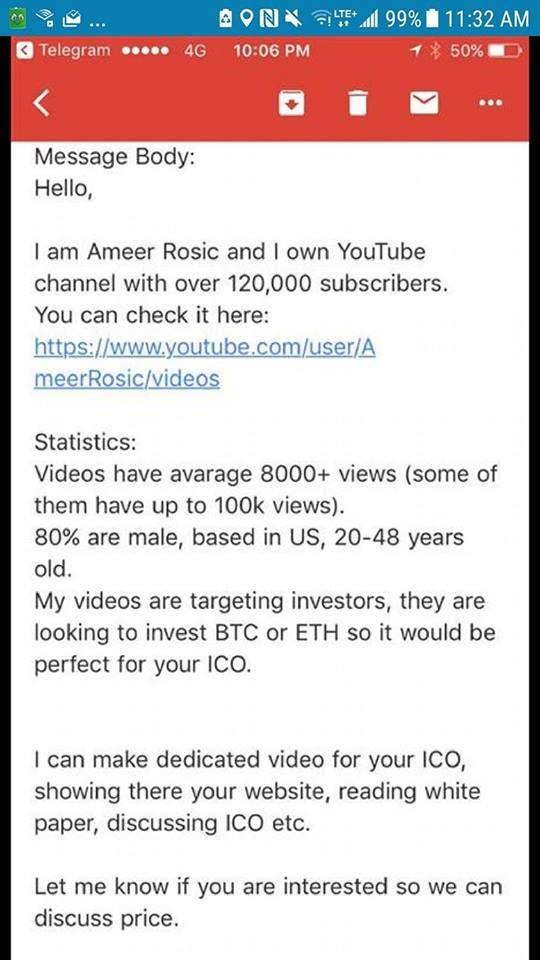
As a developer, you need to be very very very careful of this. Imagine giving away your card details or, more importantly, your key details just before your ICO! Obviously, the investors get scammed more than the developers. One of the more popular ways of scamming investors is by creating a fake social media profile which somewhat resembles the real ICO page and then manipulating potential investors to send money to their address.
Mismanagement Of Keys
If you are a developer, then there are 3 questions that you need to ask yourself:
- Where are you storing your private keys?
- How are you protecting your wallets?
- How are you protecting your customer’s tokens on your ecosystem?
- Who are you sharing your multi-sig wallet keys with?
If you are a developer, then one of the many doubts and fears that you will face from your investors is what is stopping you from running away with all of their funds? Which is a very valid question. The way that you can allay these fears is by using a multi-signature wallet.
What is a multi-signature wallet?
The easiest way of understanding how a multi-signature (multi-sig) wallet works like is by thinking of a safe which needs multiple keys to operate. A multi-signature wallet is great for 2 purposes:
- To create more security for your wallet and save yourself from human error.
- To create a more democratic wallet which can be used by one or more people.
How does multi-signature wallet save you from human error?
Let’s take the example of BitGo, one of the premier multi-sig wallet service providers in the world. They issue 3 private keys. One is held by the company itself, one is held by the user and the third one is a backup that the user can keep for themselves or give to someone trustworthy for safe keeping.
To do any sort of transaction in a BitGo wallet you will need at least 2/3 keys to operate. So even if you have a hacker behind you, it will super difficult for them to get their hands on 2 private keys. And on top of that, even if you lose your private key for whatever reason, you still have that backup key that you had given to your friend.
Now, how does a multi-signature wallet create a more democratic environment? Imagine that you are working in a company with 10 people and you need 8 approvals in order to make a transaction.
Using a software like Electrum you can simply create a custom multi-sig wallet with 10 keys. This way you can make seamless democratic transactions in your company. And that is exactly how you will allay fears regarding the safety of the investor’s money. Suppose you publicly declare that 5 of those keys will be given to neutral parties who are reputable members in the crypto environment that will obviously create more trust among the investors.
However, despite all this, even a multi-sig wallet is prone to a hack attack. A wallet is only as secure as the code that makes it. On July 19th, a vulnerability in the Parity Multsig wallet was exploited and hackers made do with $30 million in ether.
So next time you are about to hold an ICO please make sure that you are taking care of your security. No one wants to see a tweet like this:
Conclusion
ICOs are the “in thing” now and the number of ICOs held per month is increasing exponentially:
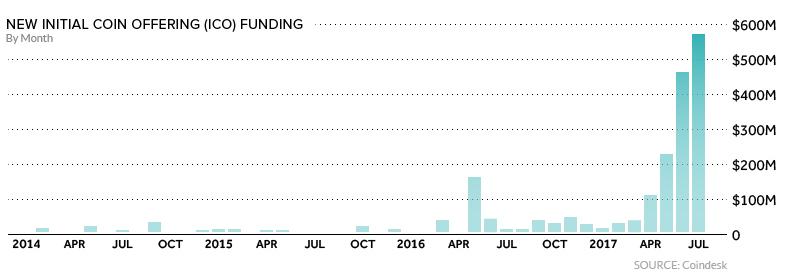
Image Courtesy: Investopedia
If you are a developer then, and there is no easy way of saying it, you will most likely fail to create an end product. Does this mean that we hate ICOs? We don’t. Like we said, we really think that it is revolutionary. But, if you are a developer then it is your responsibility to you, your potential investors, and to the future of cryptocurrency itself to use the ICOs as a means of creating something truly meaningful rather a method of making a lot of cash.
- Why are you doing your ICO?
- Is your token something that will bring genuine value?
- Are you sure you are not doing this just to make a quick buck?
If you cannot convincingly answer any of these questions then please, do not do your ICO. Don’t contribute to this “bubble”. Make something meaningful. Make something that will add to the environment, not exploit it.






The crypto market has gained good support, therefore the price will keep going upwards. This means, there’s no time as perfect as now to invest in cryptocurrency. What is cryptocurrency trading? How can you earn millions from bitcoin trading? everyone wants to know about these secrets. If you want to become a successful trader then you must have to learn the basics of crypto trading. You must learn about the fundamentals aspects of bitcoin and cryptocurrency.
If you are reading this, then you are an early adopters and investor of bitcoin. Most of the time we cannot make money from trading because we do not know how to do proper trades. sometime we apply wrong strategies while trading and sometime we do trade just based on guesses. Specially in beginner level we buy the altcoins at high prices and as a result of this, we welcome losses.
Ready to start up cryptocurrency trading? I will show you how I make good profits with my invested funds. Contact me via (Norrelsmith8@gmail.com) and l’ll show you how l earn profit over 30K in 2 months and the secret behind it for successful investment.
This is very detailed. Thanks.
I’m afraid to participate in new projects, there are many scams
That was the single most informative read I’ve encountered since I started diving in to this subject. I really appreciate the economic and financial perspective you take, which seem to be totally absent from most white papers I encounter. I really like your thinking. Hit me up if you ever want to bounce an idea off an MBA.
Very good read 😉 Thanks a lot!
Good article. I’m new to all this, and struggled to understand a couple of points. But I’ll re read the article and hopefully the points will become clearer. 🙂
Thank you for this article. its awesome!
But if you want get some help, use a team of profies!
Link here : https://olshansky.ua/ico-marketing-consulting-service
Loved this. Thank you for posting. Recommended reading for all new investors.
very nice article… it sounds like a lot of companies are actually setting up an ICO purely for a chance to receive investment but don’t consider what functionality their token actually has…should this be putting crowd funding sites on alert that their days are numbered ?
Great value! Thanx!
Just to share some live experience: I am just reading a whitepaper and the real problem is that these systems are are from being pure software products. Getting the software architecture is one thing but as soon there is token that can issue a second token and perhaps a third one, the whole market dynamics can be so complex that I think it is almost impossible to predict what is gonna happen (or at least you need a PhD from microeconomics and a year to analyse :).
Good article and points.
However too much doom and gloom IMO.
First of all I think 99% is an exaggeration. And I’m not here to nitpick. However I think it will be more between 95% and 98%.
The 5% to 2% that succeed will be worth billions even tens of billions and will offset a lot of the losses from the losers.
The dot com era gave us: Amazon, Ebay, Paypal, Google etc…
It will be a similar dynamic.
As an investor in crypto for the last 4 years I’m recently seeing an influx of quick money schemes tied to the recent increase in prices affecting bitcoin and other currencies. I’m receiving 10 requests a day on new ICO sales which are frankly get rich schemes. This is an excellent article and brings light to how many are undermining the importance of bitcoin and the blockchain as a whole. Imyself have been comparing this to the dotcom bubble of the nineties.
Great article.
I basically agree, I would just highlight one aspect of the ICOs that usually does not get enough attention.
Bitcoin is sometimes regarded as a way for financial inclusion, considering the about 2 billion people in the world who do not have access for a bank account.
And well, Bitcoin is really a technology that can be used for transferring money only with a mobile phone, without bank accounts or personal identification, providing a way for financial inclusion for everyone.
However, let we just stop for a second and think it over if financial inclusion does not only mean transferring money but getting money for a new business.
How many people in the world do have the realistic (!) possibility of raising money from venture capitals ?
200 million ?
Perhaps only 100 million ?
So what about the other 7.3 billion ?
Bad luck ?
Wrong location or education ?
I do aware that ICO-s and tokens are pretty much the wild west at the moment and performing pretty badly,
but despite I think this is eventual the technology that can disrupt the whole investment industry and gives financial inclusion for a lot of people not only in money transferring but in money raising as well.
Fair points,
The space is evolving and it will take time to figure out new models, both for entrepreneurs and also investors.
My issue, and I am approaching this from both being a serial entrepreneur and angel investor is this…
As an entrepreneur, you have two things to worry about.
Product market fit and profits, that’s it. Without those, you fail and die.
As an investor you get equity or you get rev share or you get royalties. Many ways to split it. Which leads me to your point.
Currently in the ICO space there are 3 major PROBLEMS
#1. No product fit. 99% of theses ideas dont solve any real problems in the marketplace
#2. Me as an investor in an ICO what do I really get? At the moment nothing but a manipulated token that can and will die
#3. The most important as you pointed out is… Education. This is the BIGGIE! The giant elephant in the room. We need to educate more people for the new economies we want to build. From entrepreneurs to investors and the rest.
I agree with all your points and I have spent a lot of time looking at ICO’s and general cryptocurrencies that bring something to the table. The four I have identified are bitquence, InvestFeed, Status and Elixir. I do think they each offer something unique but I wondered if I could get your perspective on them as your knowledge in this sector will provide me with insight and at the very least point out something I missed.
Hi Ameer, I am new to this ICO world and trying to find a way to launch a ICO. Our ICO does fit your tight criteria. It is has a real solution in the marketplace. In the world. And there is a true value to the investors. I know everyone says that. Everyone believes that. But if you were to hear ours you would agree it is needed and does have value. It is not another blockchain technology, it is a real world solution. So how do you get this word out and try and launch it when the article above warns you, rightly so, to be careful of who you explain your ICO to? I have been warned that people can completely clone a ICO and take investors money. How do you find trustworthy people? And when you do find the reputable trustworthy people in the blockchain and cryptocurrency industries, how do you get any of them to listen to someone accomplished in the business world but very new to the blockchain cryptocurrency world?